How to restrict access to the K2 smartforms Designer using Internet Information Services (IIS)
KB001309
PRODUCT
Introduction
This article describes how to restrict access to the K2 Designer using Internet Information Services (IIS). Follow the steps below to set up authorization rules in IIS to give specific groups or users permissions to access the K2 Designer.
If you are using K2 Five or later, you can use K2 Designer settings and the Authorization Framework in the K2 Management Site to restrict and manage access. See the Authorization Framework topic in the user guide for more information. If you want to use Internet Information Services (IIS) Manager to restrict access, you need administrative knowledge and permissions in IIS.
Procedure
Use the steps in this topic to restrict access to the K2 Designer to users and groups by adding authorization rules in Internet Information Services (IIS) Manager. Only groups and users which have been granted access will be able to open the K2 Designer site.
In addition to the specific users/roles/groups you want to add to the authorization rules, you also need to add:
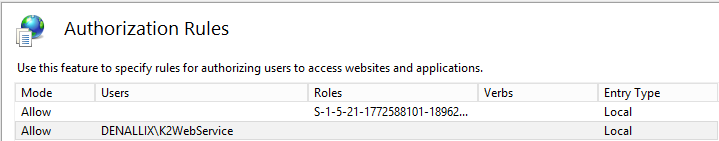
- All application pool user accounts for the application pools used to run the K2 websites
- The K2 service user account
Accessing IIS Authorization Rules
- Navigate to Start > All Programs > Administrative Tools > Internet Information Services Manager
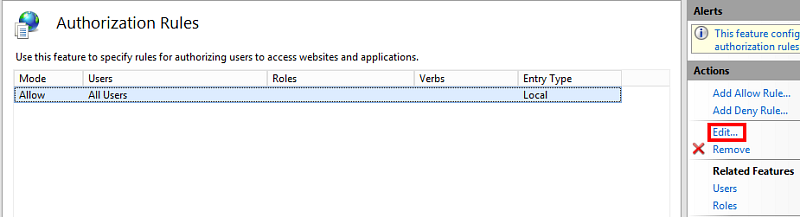
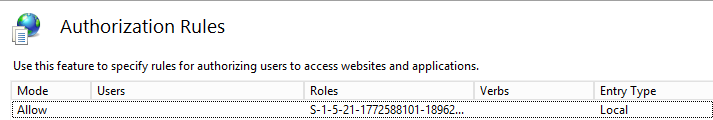
- In IIS Manager, locate the Designer site and double click the icon Authorization Rules
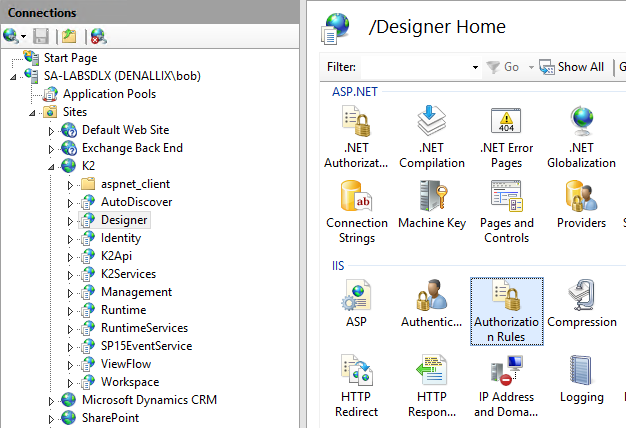
- Select the Allow All Users rule and click Edit on the right in the Actions section
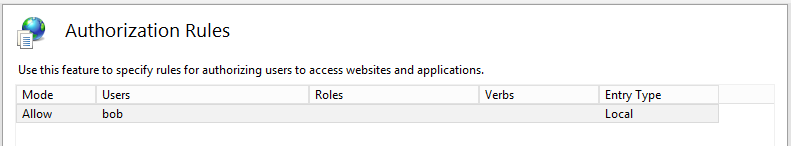
Adding Users
- Select the option Specified users and type the user name.
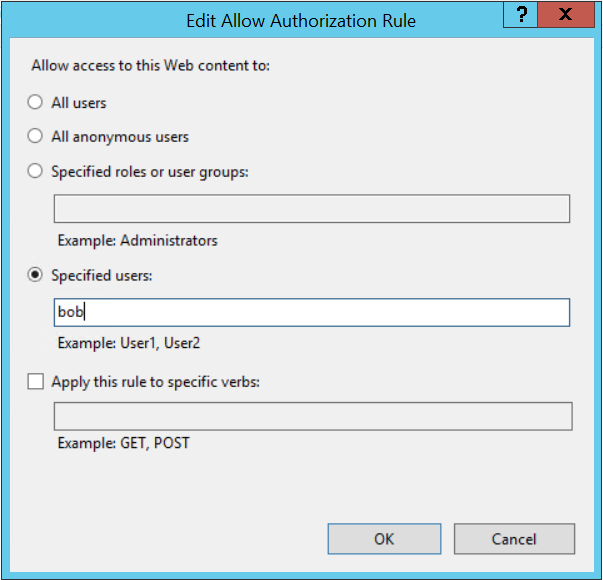
- Click OK. The specified user will now be able to access the K2 Designer site.
Adding Groups
Internet Information Services 8
When you use IIS 8, the GroupSID is required to add a group. Install the AD module for Powershell and run get-ADGroup -Identity "Group_name" to get the GroupSID value. Alternatively, use this Powershell script without installing the AD module to get the GroupSID value.
For example
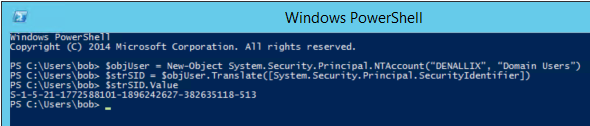
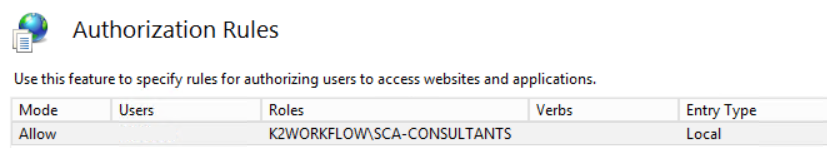
- In IIS, select the option Specified roles or user groups then copy and paste the GroupSID from Powershell.
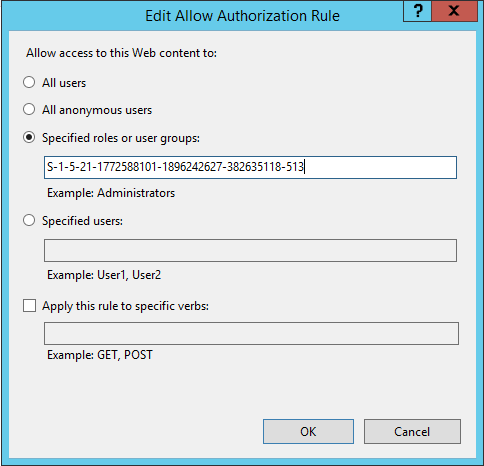
- Click OK.
Internet Information Services 10
When you use IIS 10, add a group using the DOMAINGroupName format as shown below.
- In IIS, select the option Specified roles or user groups then provide the DOMAINGroupName.
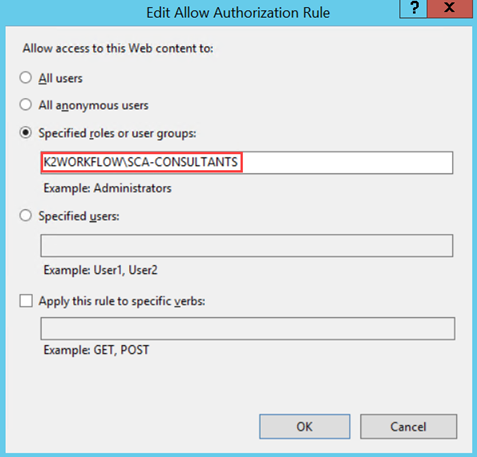
- Click OK.