How to configure K2 smartforms Runtime for Forms Authentication on a non-domain environment
KB001357
PRODUCT
Introduction
K2 smartforms Runtime can be set up on a separate workgroup server in a DMZ for SQLUM users while the K2 environment is using Active Directory authentication. This article describes how to configure K2 smartforms Runtime for Forms Authentication on a non-domain environment.
Assumptions
The following is assumed when working with this scenario:
- A working K2 blackpearl environment is configured.
- SQLUM is configured.
- The machine is in workgroup mode. If it is in domain mode, the setup pages you see here are different.
Implementation Details
Follow the steps below to implement the scenario as described above.
- Install K2 blackpearl.
- The following message is displayed. Click OK.
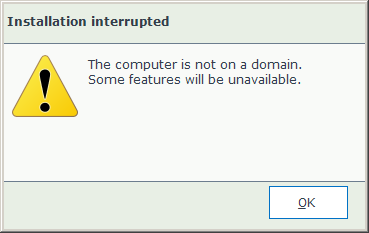 This message does not display in K2 4.7 and later.
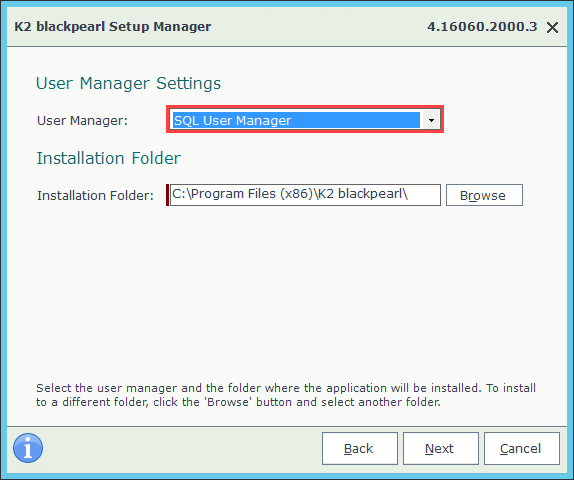
This message does not display in K2 4.7 and later. - Continue with the Setup Manager until you reach the User Manager Settings screen. Select the SQL User Manager.
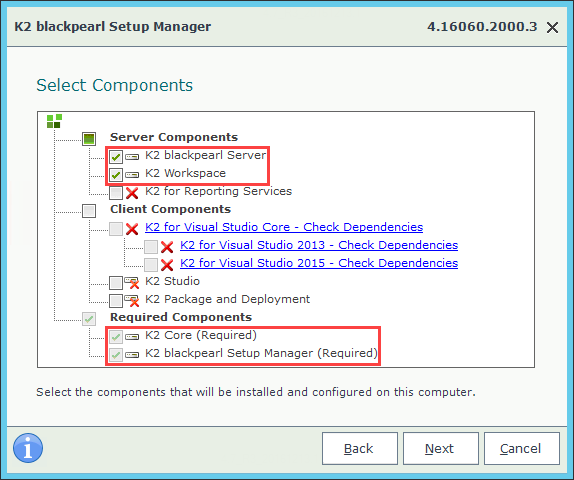
- Install the K2 blackpearl server, K2 Workspace and K2 Core components.
- Complete the Setup Manager.
- Set up the Application Pool Account by opening the Server Manager.
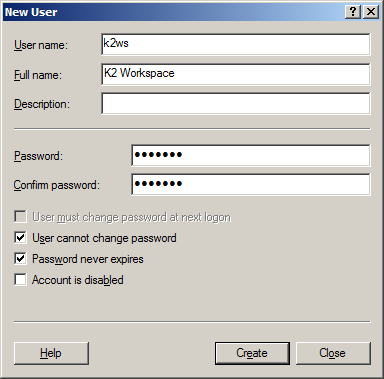
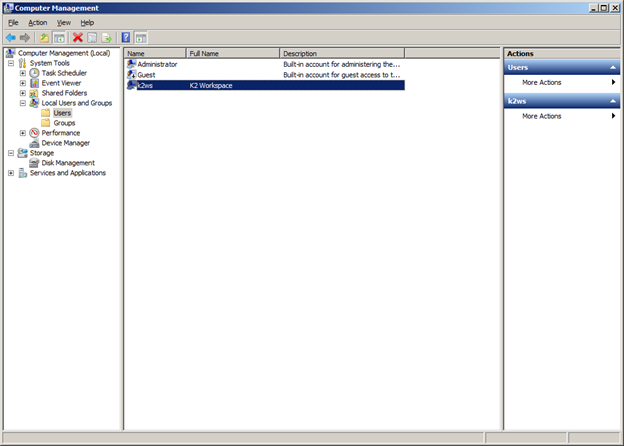
- Navigate to Configuration > Local Users and Groups > Users. Right click and select Add New User.
- Provide details for the Application Pool Account and click Create.
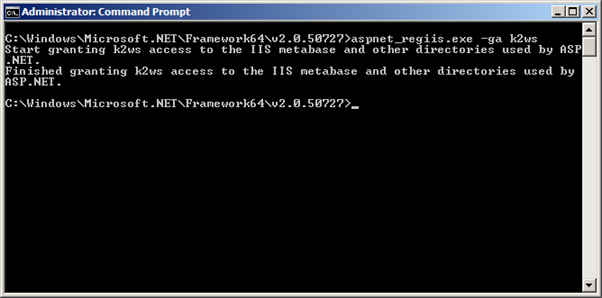
- Grant IIS (Internet Information Services) permissions for the account to run as an Application Pool with the command aspnet_regiis.exe -ga k2ws.
- Perform all other configuration required to have a successful working K2 blackpearl environment.
- Install K2 smartforms. The following message is displayed. Click OK:
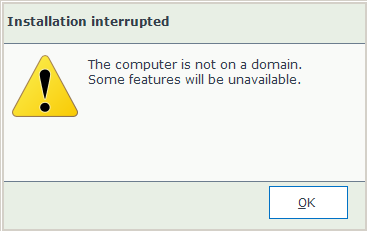 This message does not display in K2 4.7 and later.
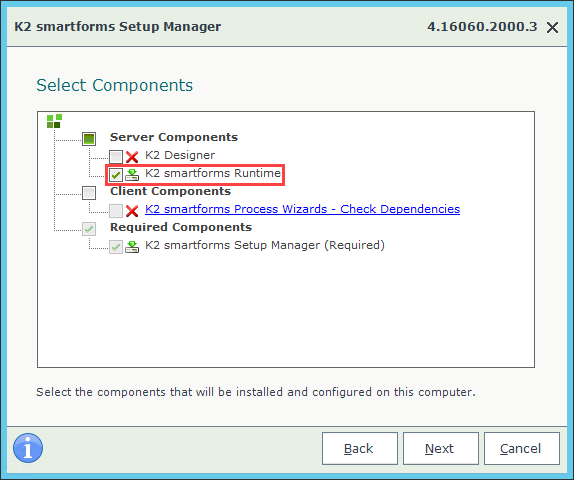
This message does not display in K2 4.7 and later. - Continue with the Setup Manager until you reach the Select Components screen. Select the SmartForms Runtime component.
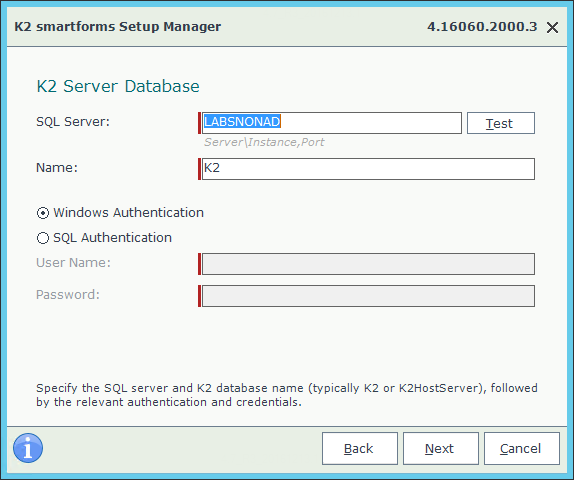
- Provide the SQL Server details on the K2 Server Database page.
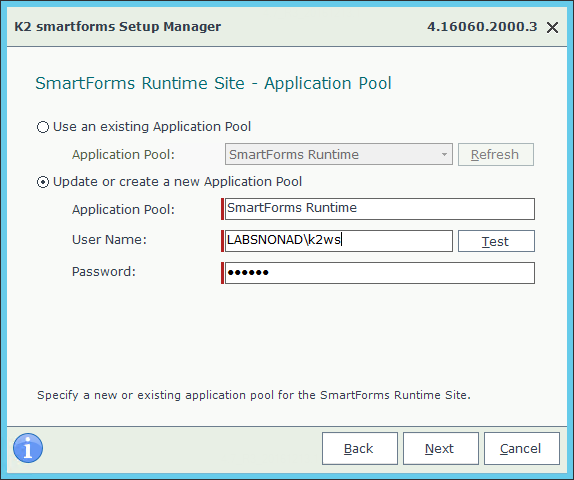
- Continue with the Setup Manager until you reach the SmartForms Runtime Site – Application Pool screen. Select the option Update or create a new Application Pool and provide the details as previously configured.
- Complete the Setup Manager.
- Make a backup of the web.config file in the K2 smartforms Runtime folder:
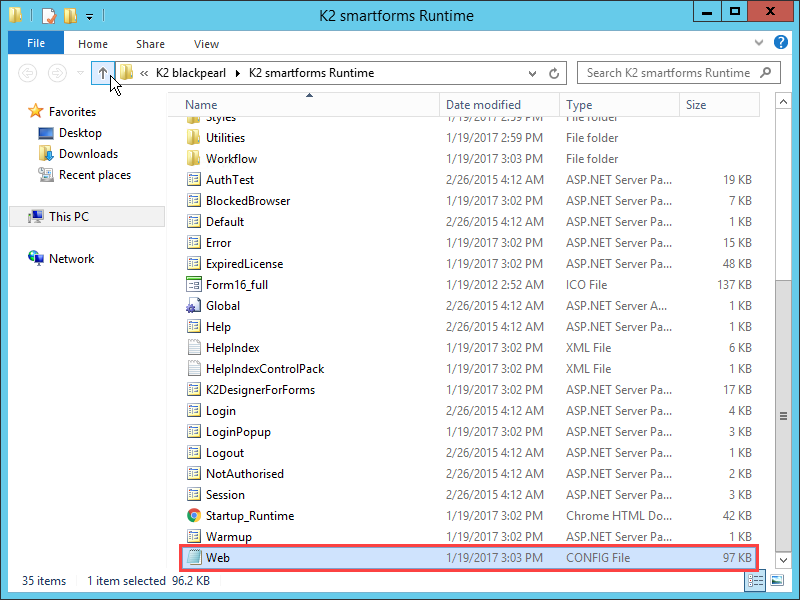
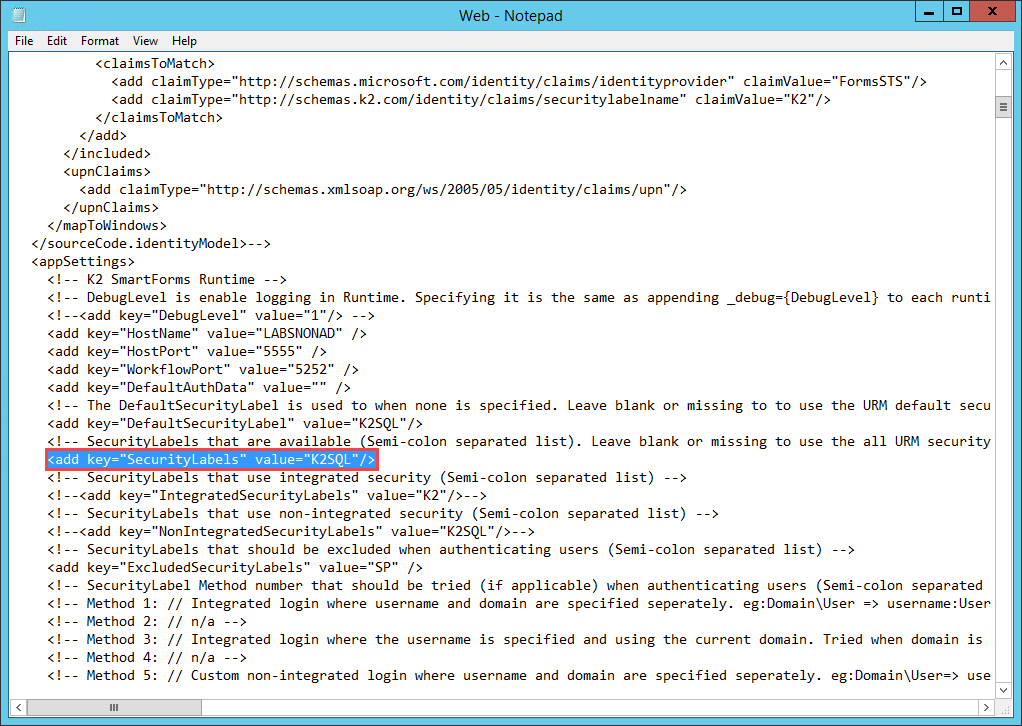
- Edit the web.config file and set the default security label to K2SQL in the node as shown below. This will allow you to type the user ID without specifying the security label.
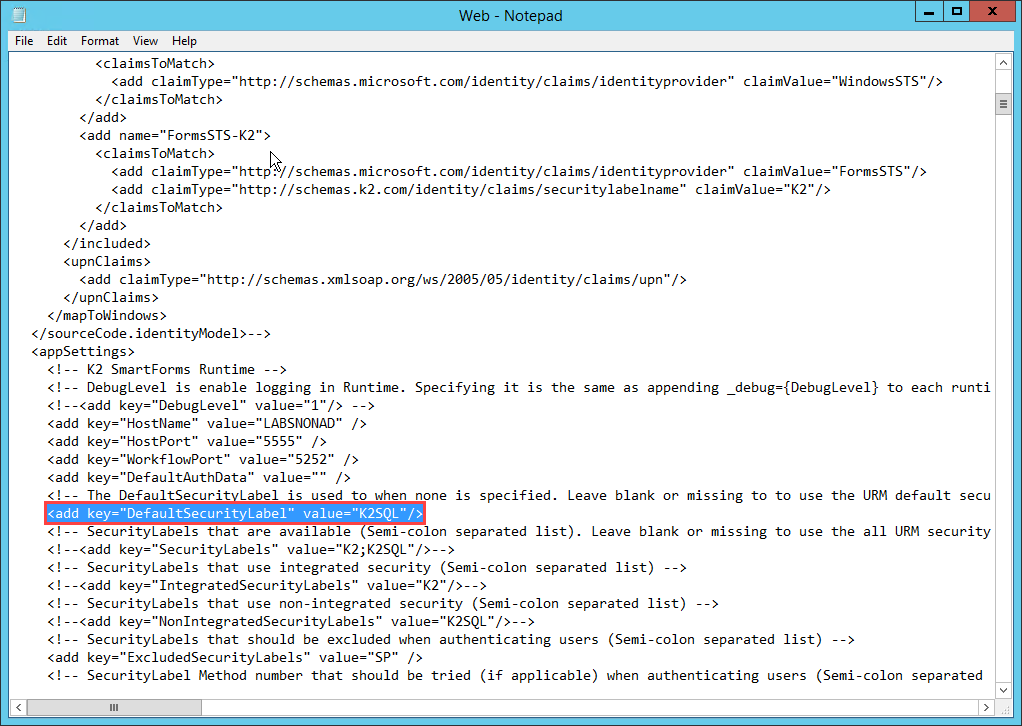
- Configure K2SQL to be the only security label in the node as shown below:
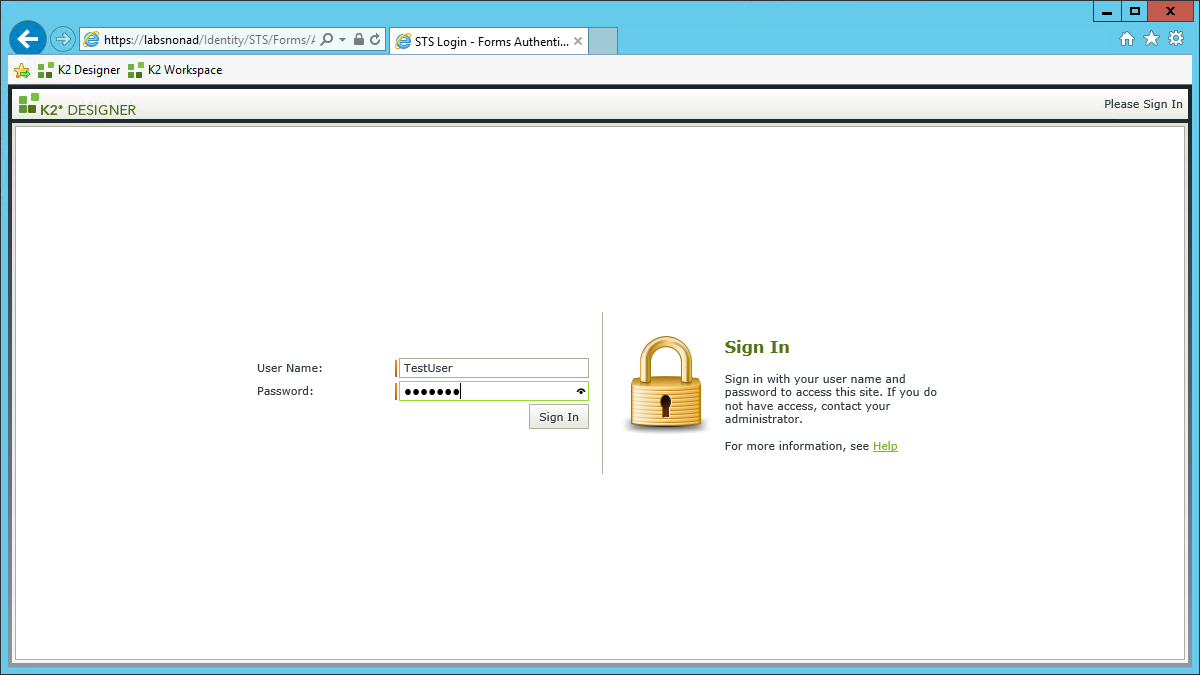
- Test the configuration by opening a Form.
Known Issue - Authentication With Server Failed: The logon attempt failed
When trying to access an external facing Smartforms Runtime site hosted on a DMZ server which is not part of a domain, an Authentication With Server Failed: The logon attempt failed error occurs:
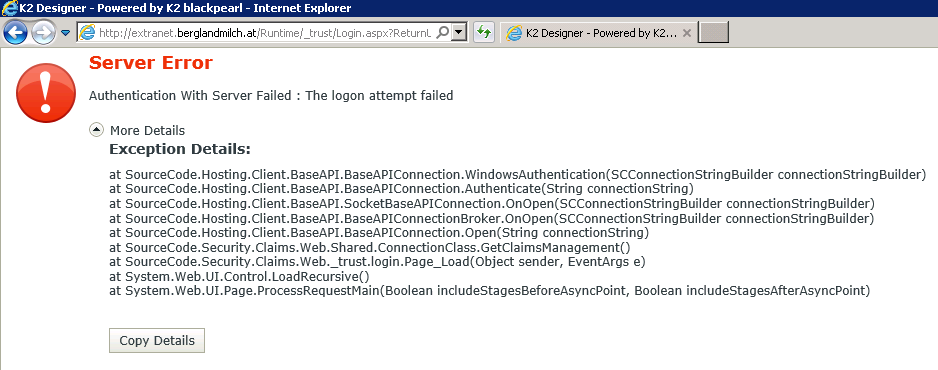
This error occurs when the Claims Authentication model is used on the DMZ server. When the SmartForms Runtime Site hosted on the non-domain DMZ server trys to authenticate, the error occurs because the workgroup identity from the DMZ server is not known by the AD-based K2 server on the internal network.
Workaround for this issue
To resolve the above issue, you can use Anonymous Authentication on the SmartForms Runtime site hosted in the DMZ server. If Anonymous Authentication cannot be used, Forms Authentication must be applied and is the recommended approach for this workaround with K2 4.6.7 and later (when claims authentication was introduced). Follow these steps to enable Forms Authentication:
- Open the Web.config file of the SmartForms Runtime site hosted on the DMZ. The Web.config file can be found in the following path: [Local Disk]Program Files (x86)K2 blackpearlK2 smartforms Runtime Web.config.
-
Comment out the following three sections in the Web.config:
<!--
<configSections>
<section name="system.identityModel" type="System.IdentityModel.Configuration.SystemIdentityModelSection, System.IdentityModel, Version=4.0.0.0, Culture=neutral, PublicKeyToken=B77A5C561934E089" />
<section name="system.identityModel.services" type="System.IdentityModel.Services.Configuration.SystemIdentityModelServicesSection, System.IdentityModel.Services, Version=4.0.0.0, Culture=neutral, PublicKeyToken=B77A5C561934E089" />
</configSections>
<system.identityModel>
<identityConfiguration saveBootstrapContext="false">
<issuerNameRegistry type="SourceCode.Security.Claims.Web.IssuerNameRegistry, SourceCode.Security.Claims.Web, Version=4.0.0.0, Culture=neutral, PublicKeyToken=16a2c5aaaa1b130d" />
<certificateValidation certificateValidationMode="None" />
<securityTokenHandlers>
<add type="System.IdentityModel.Services.Tokens.MachineKeySessionSecurityTokenHandler, System.IdentityModel.Services, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089" />
<remove type="System.IdentityModel.Tokens.SessionSecurityTokenHandler, System.IdentityModel, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089" />
<add type="SourceCode.Security.Claims.Web.WIFExtensions.Saml2SecurityTokenHandler, SourceCode.Security.Claims.Web, Version=4.0.0.0, Culture=neutral, PublicKeyToken=16A2C5AAAA1B130D" />
<remove type="System.IdentityModel.Tokens.Saml2SecurityTokenHandler, System.IdentityModel, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089" />
<add type="SourceCode.Security.Claims.Web.WIFExtensions.SamlSecurityTokenHandler, SourceCode.Security.Claims.Web, Version=4.0.0.0, Culture=neutral, PublicKeyToken=16A2C5AAAA1B130D" />
<remove type="System.IdentityModel.Tokens.SamlSecurityTokenHandler, System.IdentityModel, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089" />
</securityTokenHandlers>
</identityConfiguration>
</system.identityModel>
<system.identityModel.services>
<federationConfiguration>
<cookieHandler requireSsl="false" path="/" />
<wsFederation passiveRedirectEnabled="false" issuer="http://none" realm="http://extranet.yourdomain.com/Runtime" requireHttps="false" />
</federationConfiguration>
</system.identityModel.services>
-->
<!--<add name="WSFederationAuthenticationModule" type="System.IdentityModel.Services.WSFederationAuthenticationModule, System.IdentityModel.Services, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089" preCondition="managedHandler" />--><!--<add name="SessionAuthenticationModule" type="System.IdentityModel.Services.SessionAuthenticationModule, System.IdentityModel.Services, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089" preCondition="managedHandler" />--> -
Edit in the loginUrl of the following tag to remove the _trust part of it. Change the following from:
to the following:


