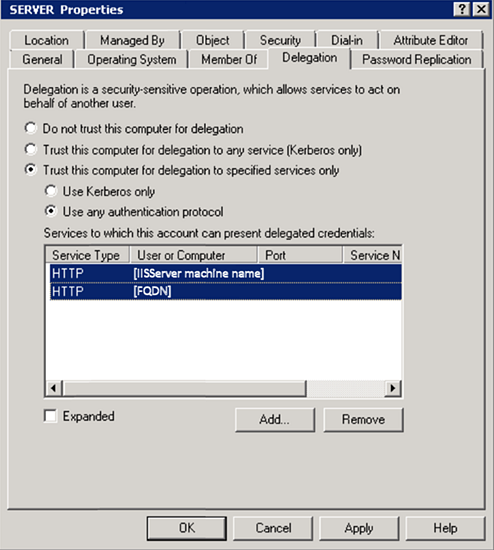
Delegation settings to enable K2 Windows Token Service to impersonate using Kerberos
KB001607
PRODUCT
Introduction
The K2 Windows Token Service (introduced in K2 blackpearl 4.6.8) is used to convert claims tokens to Windows tokens for off-box authentication and impersonation that requires a Windows token, such as SQL Server. The K2 Windows Token Service is installed on the servers where the K2 Designer, K2 smartforms Runtime and K2 View Flow components are installed, and runs under the local system account. If you use Kerberos in your environment, a domain administrator must configure constrained delegation for HTTP for both the server name as well as the FQDN for each of the following servers:
- K2 smartforms runtime server
- K2 Designer server
- K2 Workspace server (this hosts the K2 View Flow component)
Detailed Information
When K2 components are distributed between different machines or hosts, SmartObject services may require a Windows token instead of a claims token to pass user credentials between the machine boundaries. If you have Kerberos configured in your environment, constrained delegation must be enabled to allow K2 to obtain the correct Windows impersonation token on behalf of users that were originally authenticated with a claims token. The constrained delegation configuration allows a service to obtain service tickets (under the delegated user's identity) to a restricted list of other services running on specific servers on the network. The K2 Windows Token Service is a Windows Identity Foundation (WIF) feature that extracts UPN claims from SAML tokens and generates Windows security tokens. This allows K2, as the relying party, to impersonate a claims user for access to a line of business system, such as SQL.
Configuration Analysis Check
The K2 Configuration Analysis tool detects the current delegation settings against the computer account when running in an Active Directory enabled environment, and reports these values or shortcomings. It concludes with the following warning.
Constrained Delegation Settings Example
The final Delegation Properties for the server can be configured in the following screen. This must be configured on each domain where the K2 Designer, K2 smartforms Runtime, or the K2 View Flow components are installed. Each server only needs to delegate HTTP service types TO ITSELF because the service is installed locally on that server.