Known Issue: Azure Active Directory Certificate Key Thumbprint Rollover Issue
KB001807
PRODUCT
Issue
You are unable to log on to K2 sites (including the K2 Designer, SmartForms Runtime, and K2 Management sites) using AAD credentials.
When Microsoft updates its Azure Active Directory (AAD) certificates, they change the claims thumbprint. This change may prevent your AAD users from authenticating, resulting in the following error:
No valid key mapping found for securityToken: 'System.IdentityModel.Tokens.X509SecurityToken' and issuer: 'https://sts.windows.net/{YOUR_AAD_ID}/'.
You must update the claims configuration in K2 with the new thumbprint.
Resolution
To resolve this issue, update the thumbprint in the Azure Active Directory Claim Issuer configuration by following these steps:
- Open your K2 AAD app Federation Metadata Document using the following URL:
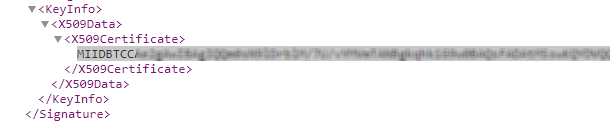
https://login.microsoftonline.com/{YOUR_DIRECTORY_ID}/federationmetadata/2007-06/federationmetadata.xml - Search the metadata XML document for a certificate value within the <X509Certificate> </X509Certificate> tags, and copy it.
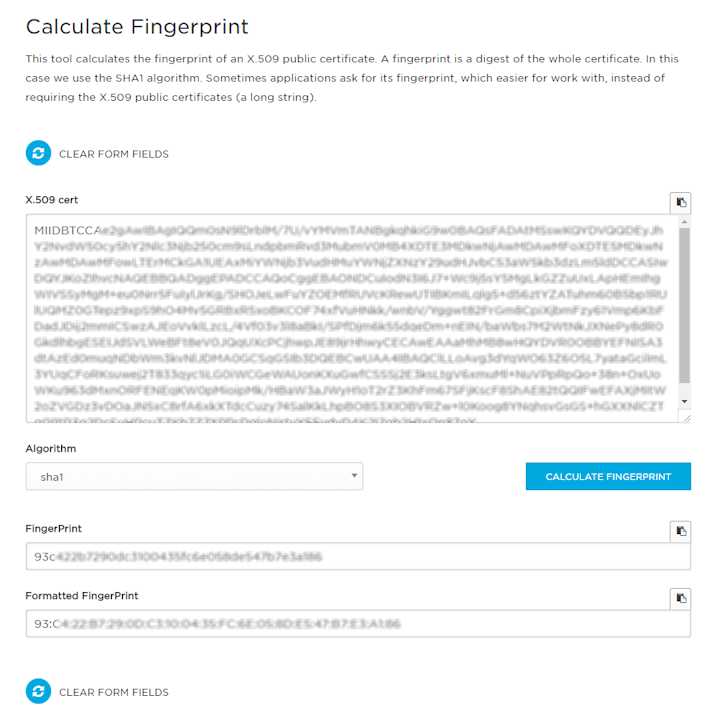
- Open the online Calculate Fingerprint tool and paste the value you previously copied into the X.509 cert field of the tool, select the sha1 Algorithm, then click the CALCULATE FINGERPRINT button.
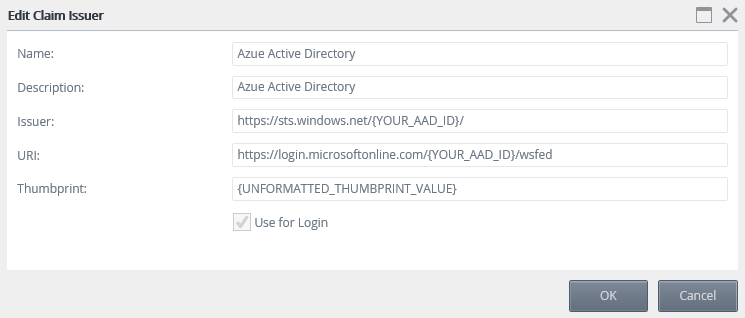
- Using your AD (not AAD) credentials, browse to K2 Management > Authentication > Claims > Issuers. Select your AAD issuer, click Edit, and paste the unformatted fingerprint value from the previous step into the Thumbprint field:
- Login to a K2 site with your AAD account. You may need to clear your browser cache.
Information for K2 4.7 systems
You may see this error on a regular basis (every two months) if you run K2 4.7 without the November 2017 CU. Be sure to apply November 2017 CU to get support for the renewal of Azure Active Directory certificate thumbprints. The November 2017 CU Release Notes mentions this change. K2 Five supports rollover of the AAD certificate thumbprints.


