How To: Use Postman to Test the Workflow REST API using OAuth
KB002838
PRODUCTUse this article to learn how to use Postman to test the Workflow REST API using an OAuth token.
Step 1: Add the K2 API Delegated Permission to your Azure AAD App
Follow the steps in Configure AAD and K2 Services for Inbound OAuth to add the K2 API permission to your Azure AD App. This is necessary for K2 to authorize the OAuth request from your AAD identity.
Step 2: Enable the Workflow REST API and get the Swagger link
In this step, you enable the Workflow REST API and get the URL to the Swagger (OpenAPI) file for the service.
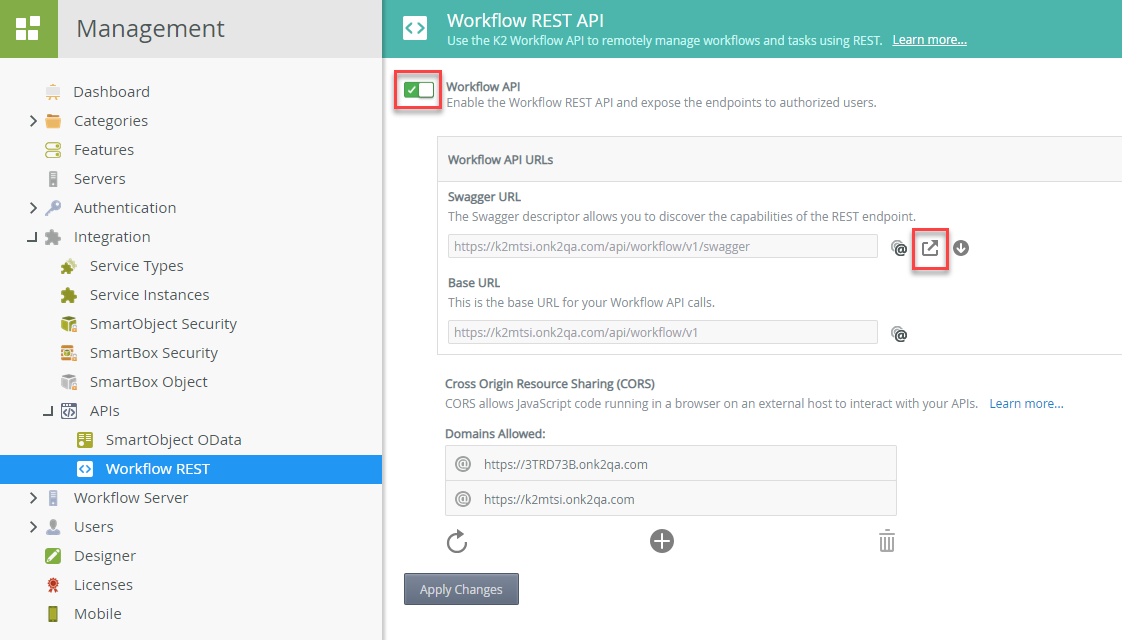
- Open K2 Management.
- Navigate to Integration > APIs > Workflow REST. Note that you can also call the SmartObject OData API with an inbound OAuth token.
- Enable the Workflow API and click the open link of the Swagger URL.
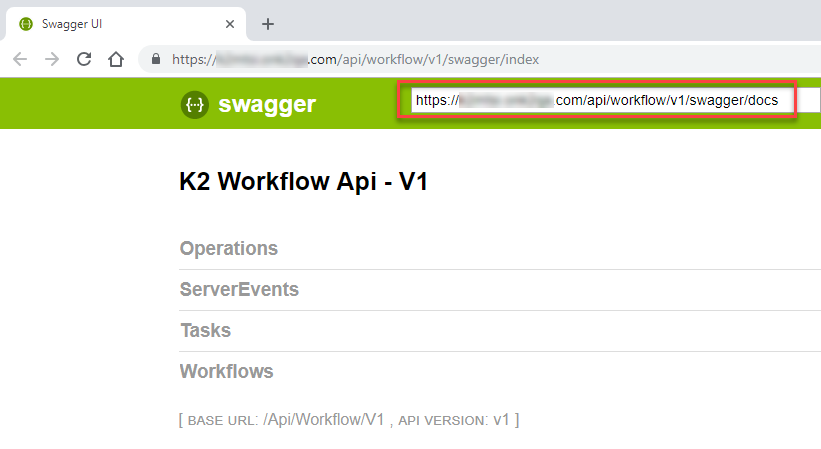
- When the new browser window opens, copy the link at the top of the window.
Step 3: Import Swagger into Postman
In this step, you import the Swagger file into Postman.
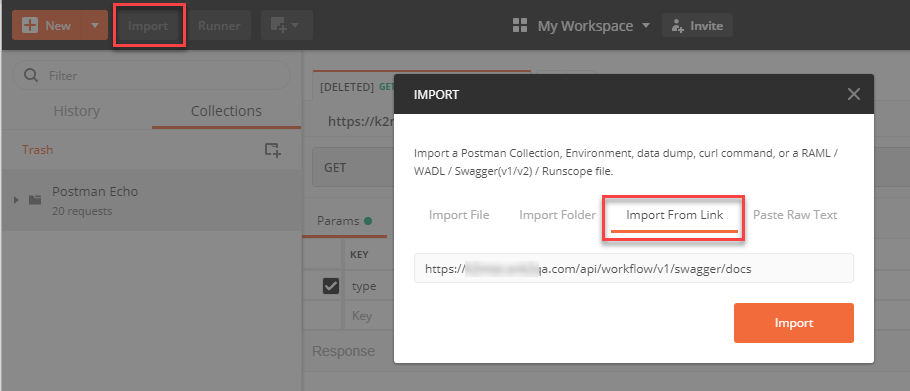
- Open Postman.
- Click Import in the upper left.
- On the Import dialog, click Import From Link and paste in the Swagger file link as shown here:
-
Click Import.
-
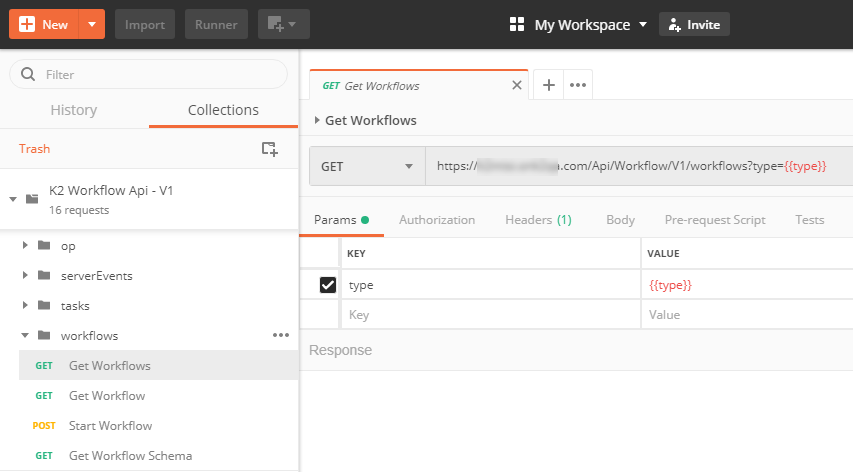
Navigate to Workflows > Get Workflows.
Step 4: Acquire an OAuth Token and Test the API
In this step, you configure Postman to retrieve an OAuth token to access the K2 Workflow REST API.
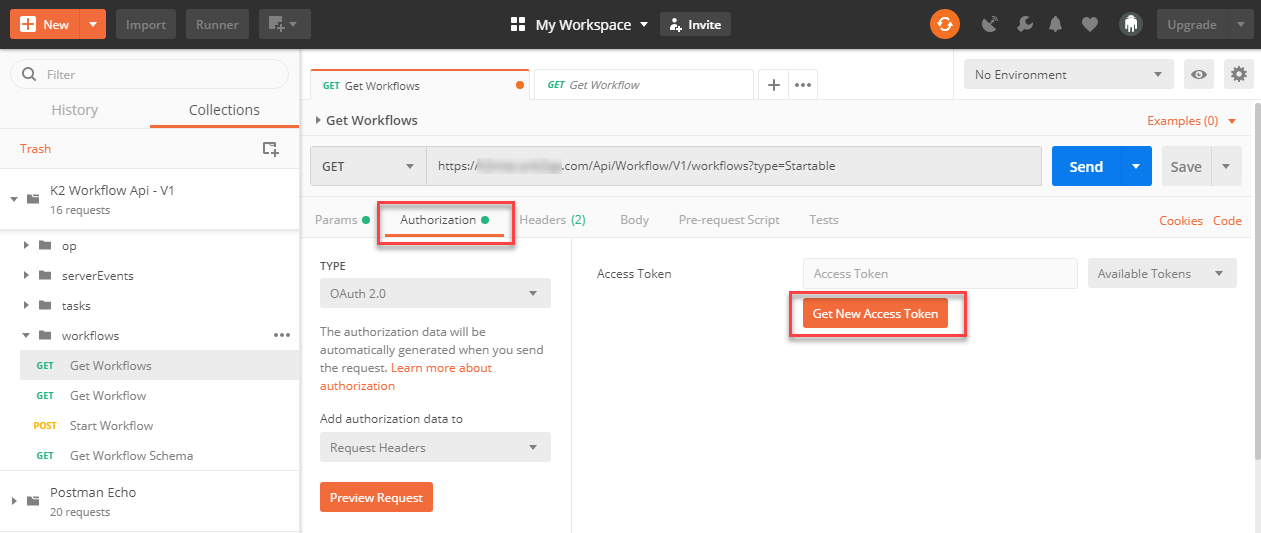
- Click Authorization and then Get New Access Token.
- On the Get New Access Token dialog, fill in the values for your environment:
| Field | Example Value |
| Callback URL (the reply_uri) | https://www.getpostman.com/oauth2/callback |
| Auth URL | https://login.windows.net/{Azure Tenant}/oauth2/authorize?resource=https://api.k2.com/ |
| Access Token URL | https://login.windows.net/{Azure Tenant}/oauth2/token |
| Client ID | Your app’s Client ID (Application ID), such as 433d08a8-e5c8-4784-aeb0-b0ac24af6c1c |
| Client Secret | Your app’s secret, such as k77OemePvRUURLaXBCTRUaieDNXgaaLoiohW/Md0X5M= |
- Click Request Token and log in using your AAD identity.
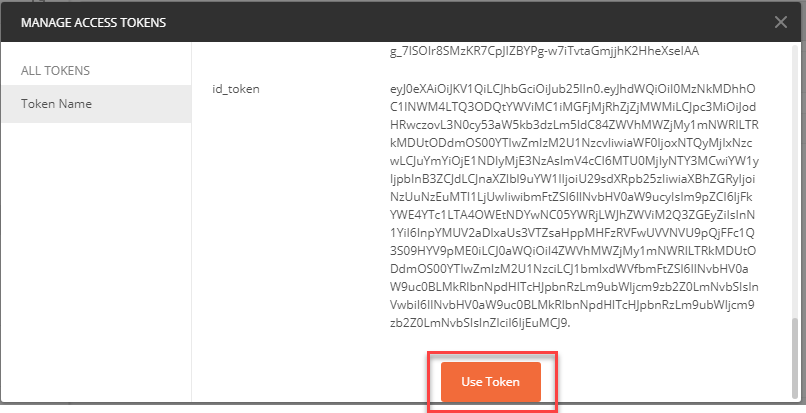
- Scroll down to the bottom of the Manage Access Tokens dialog and click Use Token.
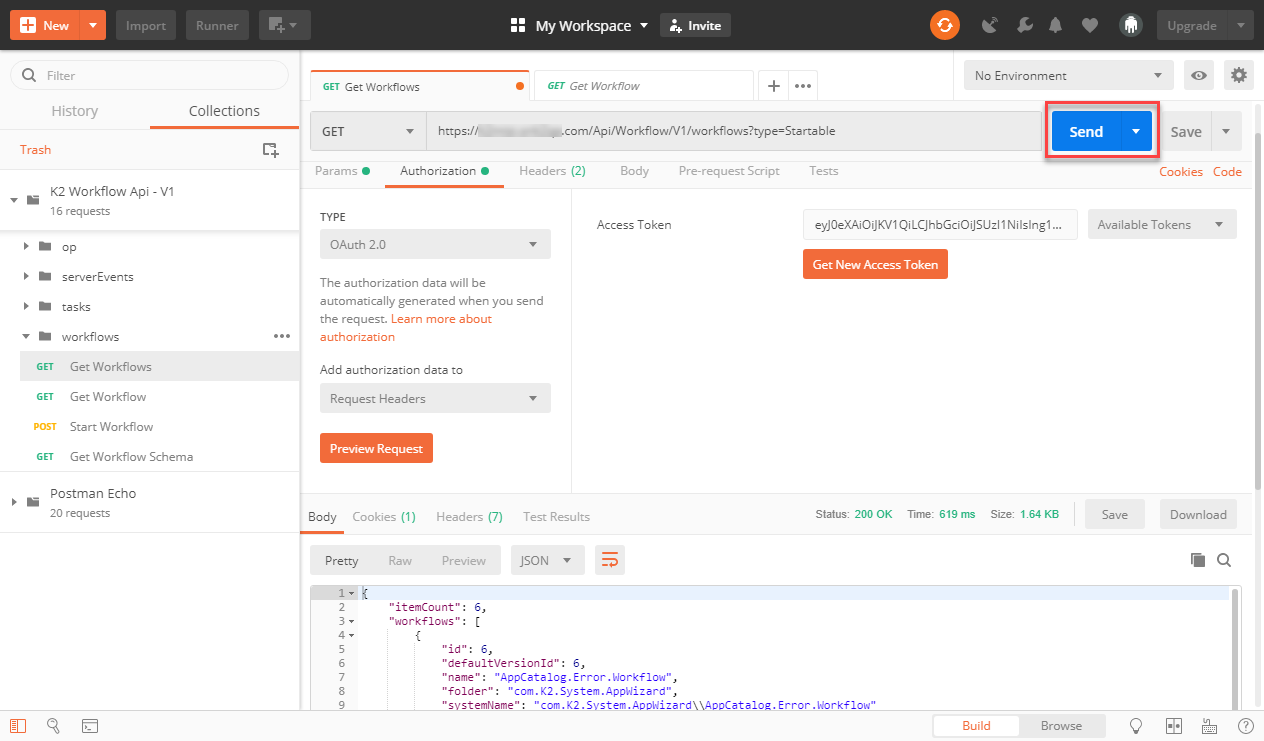
- Click Send and note the JSON payload in the Body of the response.
See Also
Use these links for learning more about OAuth in the K2 platform and code for calling K2 services.
- Configure AAD and K2 Services for Inbound OAuth
- Outbound Authorization and OAuth in K2
- K2 Five Developer Reference: K2 Five Workflow REST API code samples
- K2 Cloud Developer Reference: K2 Cloud Workflow REST API code samples


