Giving rights to users on AAD results in an error
kbt150756
PRODUCTIssue
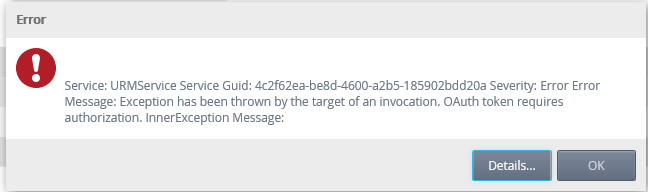
When trying to add AAD accounts to K2 5.1 the below error is presented:
"Service URMService Service Guid {GUID} Severity: Error Error
Message: Exception has been thrown by the target of an invocation. OAuth token requires authorization. InnerException Message."
Symptoms
This error relates to incorrect consent given to the admin account and not the K2 Service account as the K2 Service account and the Tenant admin need to "handshake" before all the AAD accounts will be allowed to sync up with K2 identity.Resolution
Please do the following to grant the K2 Service account consent to perform this task:
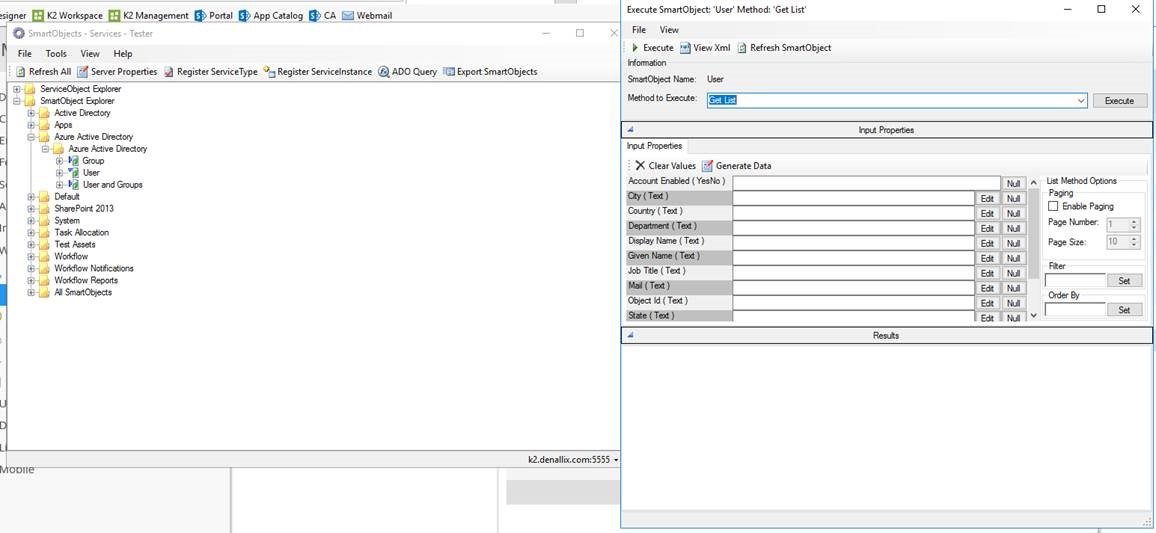
Log in with the K2 service account and go to the SmartObject tester tool and execute the following Azure SmartObject:
SmartObject Explorer > Azure Active Directory > Users > then execute with the Get List Method
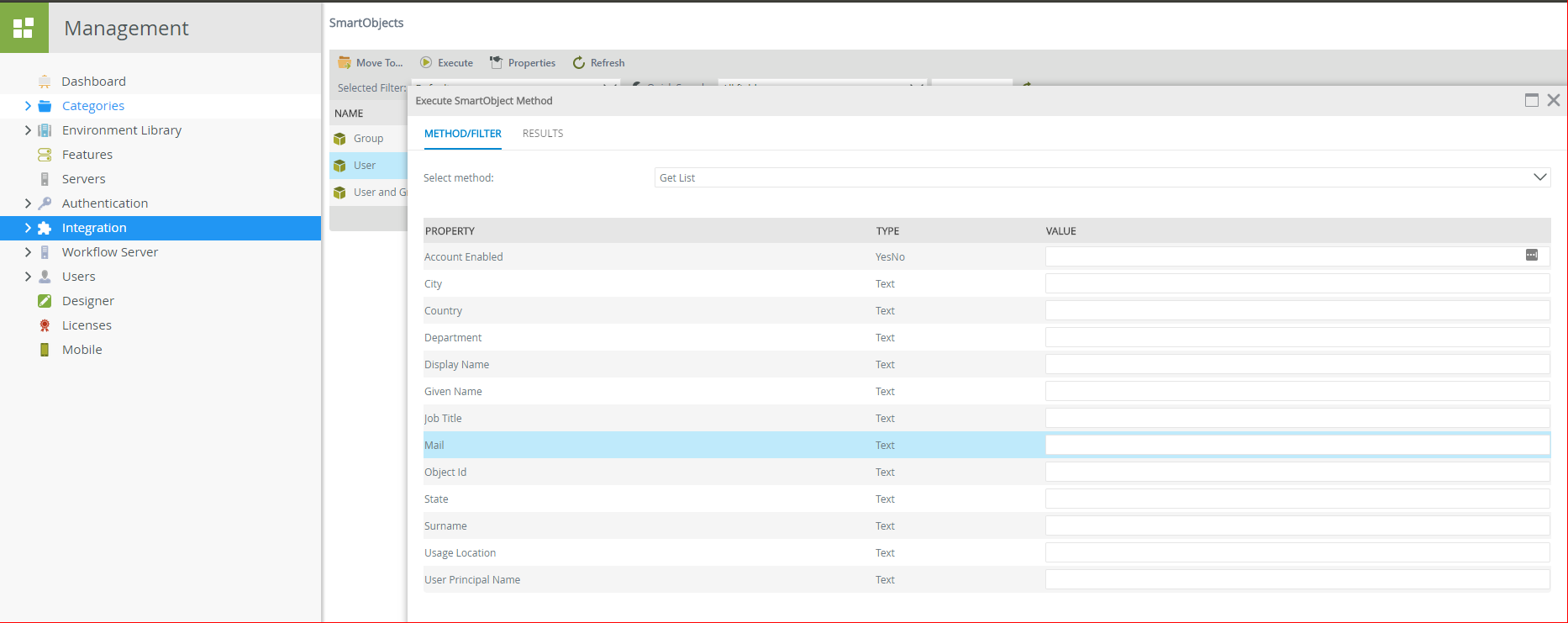
This can also be done via K2 Management:
Once this is done, grant consent for the K2 Service account using the tenant admin account.