KB001218 - How to setup Kerberos configuration to allow delegation to the LDAP server
KB001218
PRODUCT
Introduction
It is possible in a K2 distributed environment to configure Kerberos to allow delegation to the LDAP server by following the configuration steps below:
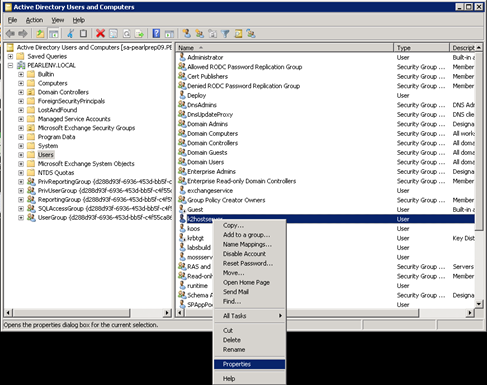
Step 1 - On the Domain Controller browse to Administrative Tools > Active Directory Users and Computers.

Step 2 - Locate the K2 Service Account User > Right-Click > Select “Properties”
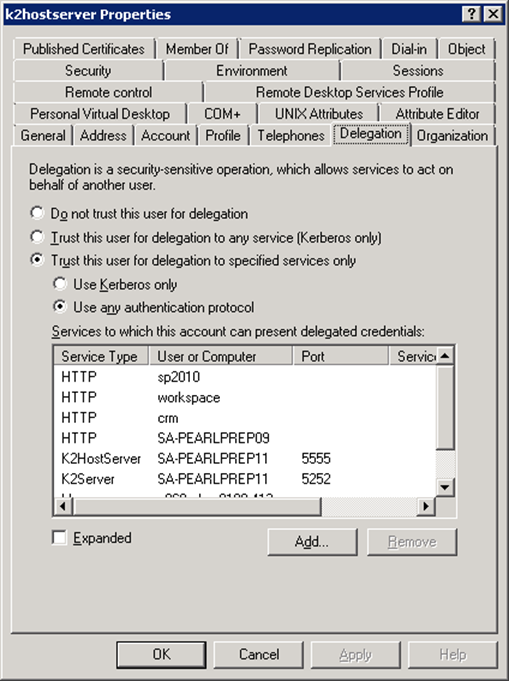
Step 3 - Select the “Delegation” tab and then click on the “Add” button.
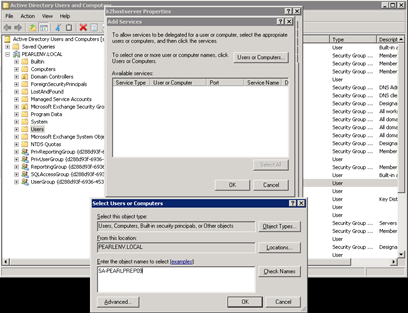
Step 4 - Click on the “Users or Computers...” button and type in the name of the Domain Controller machine and click OK.
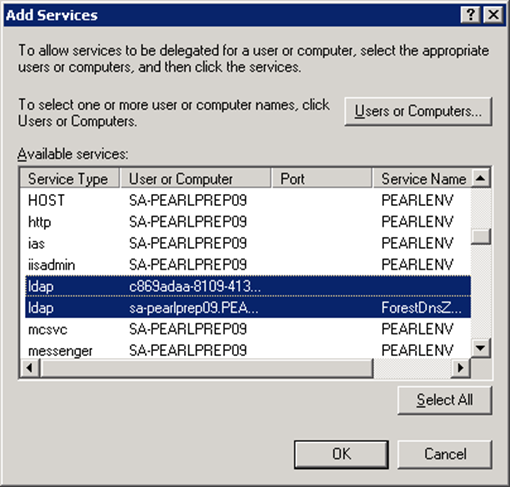
Step 5 - Locate and select the two “ldap” service types and click OK.
Step 6 - Check that the K2 Service Account user now has permission to these services.

| Important: When SETSPN –l DOMAINServiceAccount is run, these 2 protocols will NOT be listed under the user's details as these SPNs already exist and are only granted the user rights to use them. They are not explicitly created against this user's account. |


