Security Concerns with Azure-based K2 Integration
KB002827
PRODUCT
When you integrate K2 with Microsoft Online & Azure-based services, in many cases you must grant permissions using a tenant administrator account. This is due to the rights that K2 needs to integrate with services such as SharePoint Online, Exchange Online, and other Azure-based APIs.
Table of Contents
About the Azure 'Requires Admin' Permissions
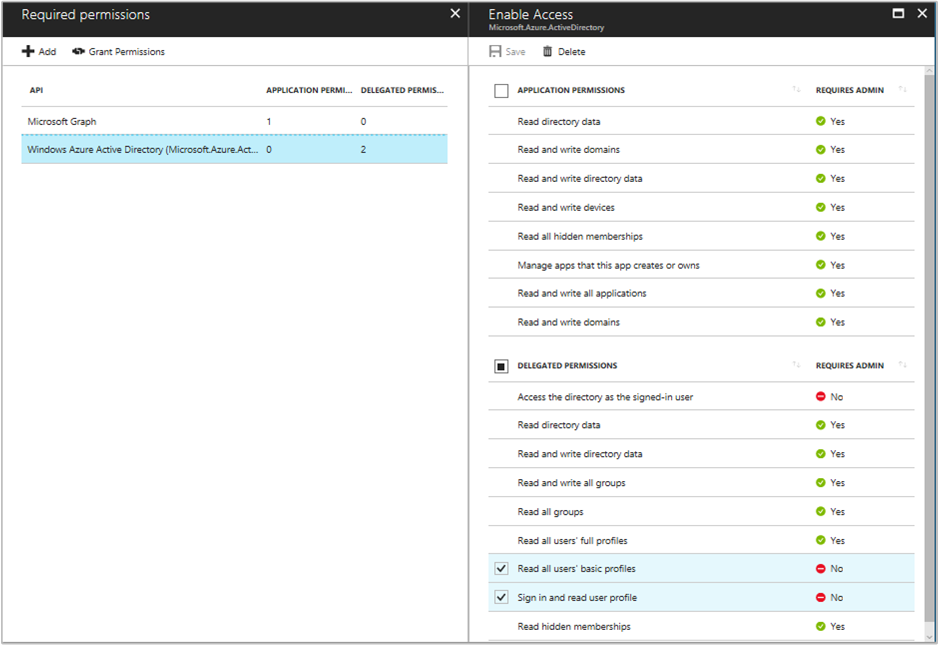
Azure includes many different permissions used to delegate functionality to another online app, such as K2. Some of these permissions require Admin approval, meaning it must be granted by a tenant administrator, while other permissions do not. For more information see Microsoft’s article Azure Active Directory consent framework. In this article is the following image. Note that the Requires Admin column shows whether a specific permission requires tenant administrator and all Application Permissions require administrator consent.
- For more information about specific required and optional Azure permissions in K2 Cloud, see https://help.k2.com/onlinehelp/K2Cloud/UserGuide/current/default.htm#Welcome/Applications.htm
- For more information about specific required and optional Azure permissions in K2 Five, see https://help.k2.com/onlinehelp/K2Five/UserGuide/current/default.htm#Welcome/Applications.htm
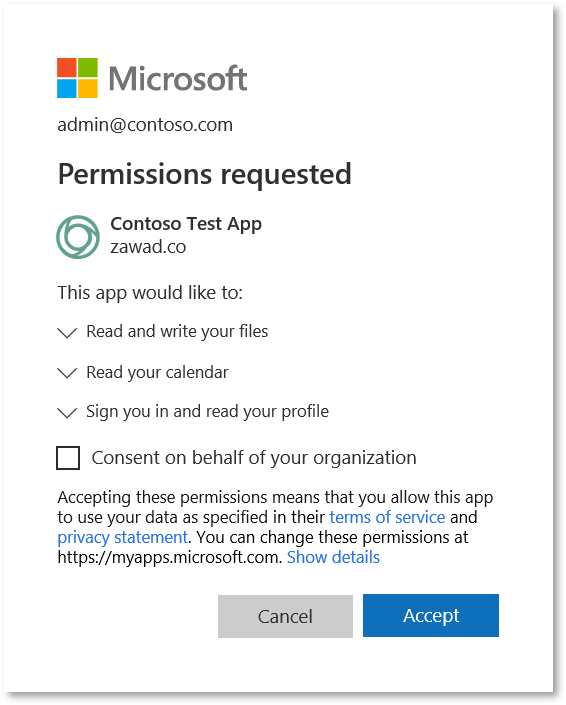
Additionally, if you’re a tenant administrator and want to consent delegated permissions for all users so that they are not also prompted to consent to the K2 app permissions, you can check the Consent on behalf of your organization option in the consent dialog as shown here (which is taken from Microsoft’s article Understanding Azure AD application consent experiences).
FAQs
The following Q&A details concerns you may have about security, authentication, and authorization.
Q: If I have not logged in to Azure before, or it has been a while since I logged in, why am I prompted for my credentials?
A: Since K2 never prompts for credentials nor does the server store passwords, these credential prompts are always from Azure. For more information about token lifetime, see Microsoft’s article Session timeouts for Office 365
Q: If I’ve consented using my tenant administrator account, why am I prompted again?
A: If the requested permissions change, such as if a K2 app is updated to include new functionality that needs another permission or Azure permissions change, you may be prompted for tenant administrator permissions again. It can also happen on upgrade or whenever you run the Registration Wizard on your app catalog.
Furthermore, if a token is being created for the K2 service account identity, which is at the scope of an application permission, K2 appends a URL parameter ?prompt=true. This ensures that the K2 service account identity can request and receive an app-only token. These are different than standard user tokens. For more information about app-only tokens, see Microsoft’s article Accessing SharePoint using an application context, also known as app-only
Q: Are tokens, permissions, and scopes all the same?
A: No, an OAuth token is a scope grant, and permissions can still be more restrictive than a token scope. While the K2 app needs to be delegated permissions that require a tenant administrator, such as Sites.FullControl.All in SharePoint, users who do not have this level of access will not automatically get it when K2 is integrated with SharePoint. Only the K2 app is granted this level of access for use in workflow steps such as Create Subsite.
Q: Can K2 request less than Full Control permissions (such as Manage)?
A: No. Since K2 integration with SharePoint uses the features in the following table, it must request Full Control.
| Permission | Description | Dependent permissions | Included in these permission levels by default |
| Manage Permissions | Create and change permission levels on the website and assign permissions to users and groups. | View Items, Open Items, View Versions, Browse Directories, View Pages, Enumerate Permissions, Browse User Information, Open | Full Control |
| Create Subsites | Create subsites such as team sites, Meeting Workspace sites, and Document Workspace sites. | View Pages, Browse User Information, Open | Full Control |
| Manage Web Site | Grants the ability to perform all administration tasks for the website, as well as manage content. | View Items, Add and Customize Pages, Browse Directories, View Pages, Enumerate Permissions, Browse User Information, Open | Full Control |
| Create Groups | Create a group of users that can be used anywhere within the site collection. | View Pages, Browse User Information, Open | Full Control |
| Enumerate Permissions | Enumerate permissions on the website, list, folder, document, or list item. | Browse Directories, View Pages, Browse User Information, Open | Full Control |
For more information, see User permissions and permission levels in SharePoint Server and Understanding permission levels in SharePoint
Q: Can K2 request access to a single SharePoint site collection (and not all site collections)?
A: No, Graph site permissions are only available for All sites and do not have this level of granularity.
For more information, see the ‘Sites permissions’ section of Microsoft Graph permissions reference
Q: Can I hide the K2 app from some site collections?
A: Yes, between app deployment and app activation, you can choose which site collections get the K2 app activated to them. For more information, see K2 for SharePoint App Registration and Activation
Q: Can I hide the K2 app from certain subsites in a site collection?
A: No. You can prevent K2 for SharePoint from being activated on new site collection by unchecking the Enable auto-activation on sites where the app is deployed option on the Manage App Activations page. If you don't enable this option, you must activate each site collection needing K2 integration from the app catalog. For more information see K2 for SharePoint App Registration and Activation
Q: Why does K2 require tenant administrator permissions to access a site collection?
A: K2 does not control what permissions AAD designates as needing tenant administrator to give consent for the permissions. As a case in point, a read-only permission scope for managed metadata requires an administrator to give consent. While this may seem a bit extreme, as consumers of these requirements, K2 has no other option than to request this higher level of consent. For more information, see the ‘Sites permissions’ section of Microsoft Graph permissions reference
The Graph API is the name of the collection of most Office 365/Microsoft Online APIs.
Q: For K2 Five, can I configure AAD without SharePoint permissions?
A: Yes, you can do this by following the Help article Manually Configure K2 for Azure Active Directory (AAD)
Resources
A list of topic links in this article included here for your convenience.
- Microsoft Graph permissions reference
- Understanding Azure AD application consent experiences
- Azure Active Directory consent framework
- Manually Configure K2 for Azure Active Directory (AAD)
- K2 for SharePoint App Registration and Activation
- Accessing SharePoint using an application context, also known as app-only
- Session timeouts for Office 365
- User permissions and permission levels in SharePoint Server
- Understanding permission levels in SharePoint
- Microsoft Graph permissions reference


