Converting K2 and SharePoint from HTTP to HTTPS
kbt132960
PRODUCTObjective
The issue experienced occurred when converting K2 and SharePoint from HTTP to HTTPS.
After the changes have been made the worklist webpart was not loading as the certificate was not a trusted certificate. I was not sure where to bind the wildcard certificate for the app domain.

Before You Begin
Obtain a wildcard certificate for the SharePoint site and K2 sites.How-to Steps
1. Obtain a wildcard certificate for the SharePoint site and K2 sites. In my case the SharePoint URL is https://domain1.co.za and the K2 urls was https://k2.domain1.co.za.
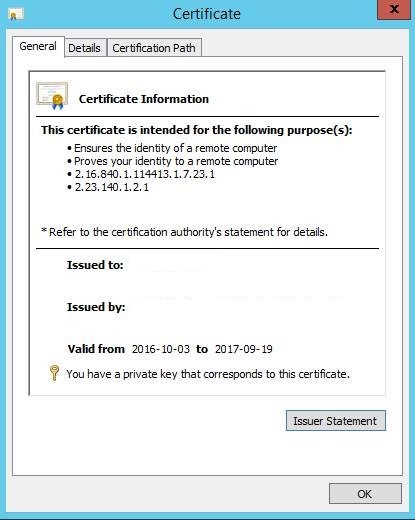
In this case we obtained one wildcard certificate from Provider which is used for the SharePoint site and the K2 sites.
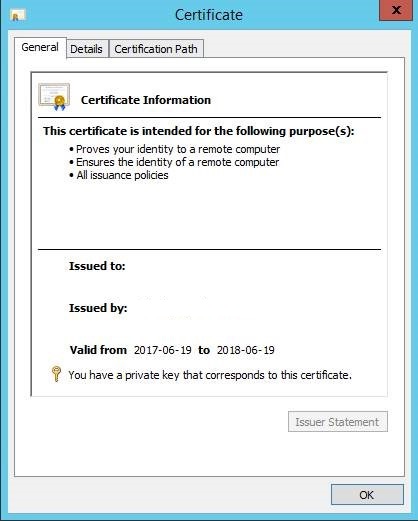
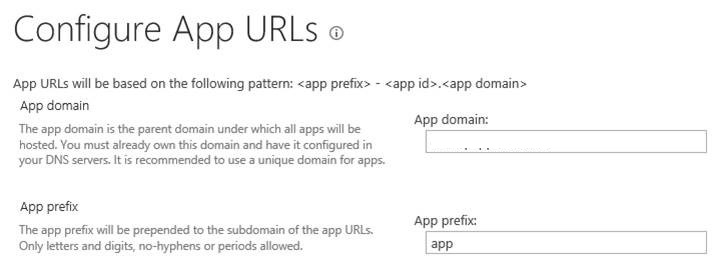
2. Obtain a wildcard certificate for the app domain (in my case *.domain2.co.za). Seeing that SharePoint handles the app redirect internally and our sites are all using host headers you need a blank SharePoint site running on HTTPS without a host header for the app redirect to function correctly.
3. The server needs to have 2 NIC’s each with a different IP address
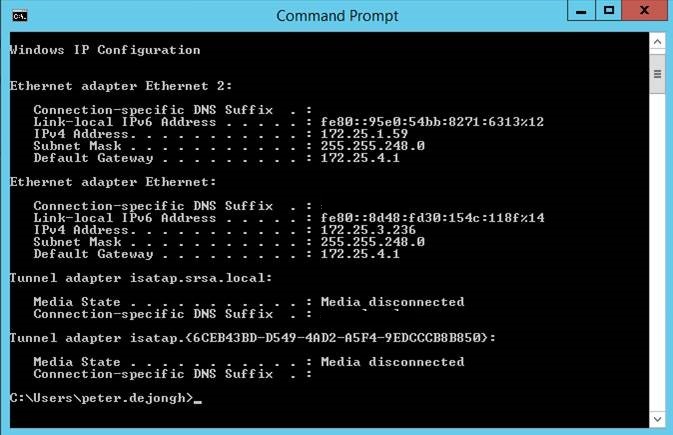
4. Create a DNS entry for the SharePoint site workflowsdev.domain1.co.za pointing to the IP address of the first NIC
5. Create a CNAME record for the app domain which in my case was dunlopappsdev.co.za. It is important that the appdomain only has one domain, and not subdomains as the SSL certificates doesn’t support subdomains. You cannot for example use the following url for the app domain appsdev..co.za as the url for the app would then be app-123456.appsdev..co.za which contains multiple domains, and would fail.

6. The CNAME record should also point to the second NIC on the SharePoint server. The reason for this is that you cannot bind 2 different SSL certificates on 2 different sites on the same IIS box running on the same port (443)
7. Now you can bind the *.domain1.co.za wildcard certificate to the domain2.co.za IIS site.
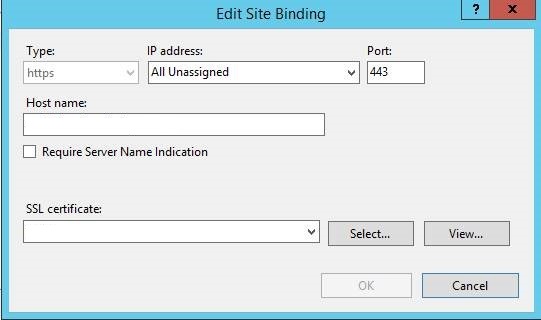
8. Now you can bind the appdomain wildcard SSL certificate to the empty web application, but bind it only for the second NIC’s ip address
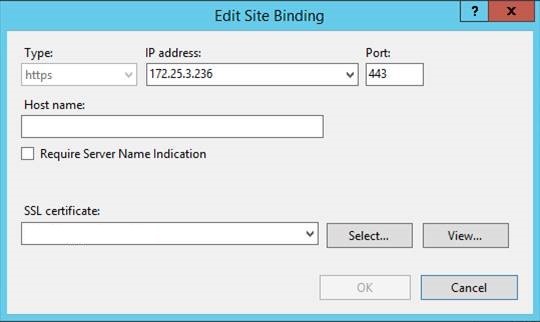
9. Important to note that we created a self-signed certificate for the appdomain. In this case we needed to add the self-signed certificate to the client computers trusted certificates by means of a login script.


