"No valid key mapping" error appears due to ADFS certificate setup in K2 table
kbt148485
PRODUCTIssue
The following error appears:
WIF10201: No valid key mapping found for securityToken: 'System.IdentityModel.Tokens.X509SecurityToken' and issuer: 'https://login.xxxx.yy/adfs/service/trust'.

Symptoms
This issue appears if you don't have a good ADFS certificate setup in K2 table [Identity].[ClaimIssuer], or this certificate is started by invalid characters.Troubleshooting Steps
To verify the ADFS thumbprint, please follow these steps:
Step 1 (Manual approach or PowerShell) is mandatory, Step 2 is preferred, Step 3 should only be done if Step 2 cannot be completed.
Step 1 Manual approach - Get the Thumbprint from the Certificate:
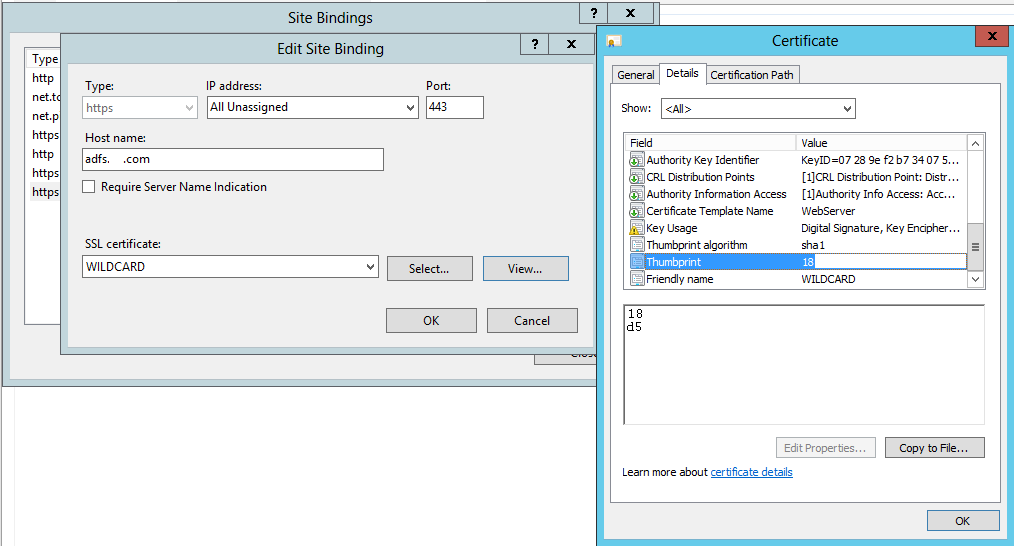
- Get the new SSL thumbprint by using MMC:
Start → Run: mmc.exe Menu: File → Add/Remove Snap-in…
Under Available snap-ins, select Certificates and click Add.
Select Computer Account for the certificates to manage. Click Next.
Select Local Computer and click Finish.
Press OK to return to the management console.
- The certificate usually resides under the following category:
-- Trusted Root Certification Authority -> Certificates
- Open the specific certificate by double-clicking or right-click and selecting Open
- Go to the Details tab
- Scroll down until you find the "Thumbprint" Field and select it
- Copy the thumbprint at the bottom and paste into Notepad
You'll notice it has spaces and consists of lower case letters.
- Remove the spaces and change all the letters to uppercase (VERY IMPORTANT - it won't work with lower case)
- Finally, copy the finished string as you're going to need it later.
Step1 (other possibility by PowerShell):
Execute PowerShell as administrator and execute the following command:
Get-AdfsCertificate -CertificateType Token-Signing
$a = Get-AdfsCertificate -CertificateType Token-Signing
$a.Thumbprint
Step 2 (up to 4.6.11)
- Update the Thumbprint in K2 using K2 Management:
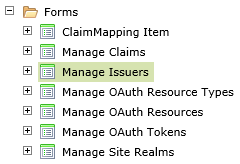
Open K2 Designer, Display System Object (Filter at bottom), All items > System > Management > Security > Forms > Manage Issuers
- Select the issuer in question
- Click the Edit button
- Update the thumbprint to the final copy created in Step 1 above - it should be uppercase with no spaces
- There shouldn't be a need to restart the K2 service, but if you don't see any immediate changes, you can restart the K2 Service and do an IISRESET
- You are finished.
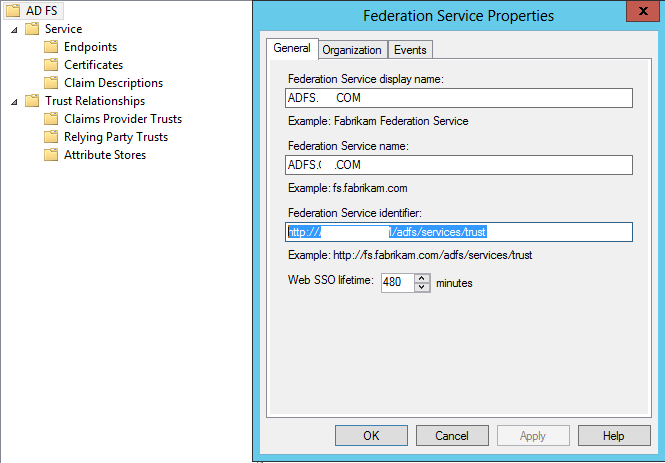
Issuer: Federation Service Identifier http://ADFS.domain.COM/adfs/services/trust
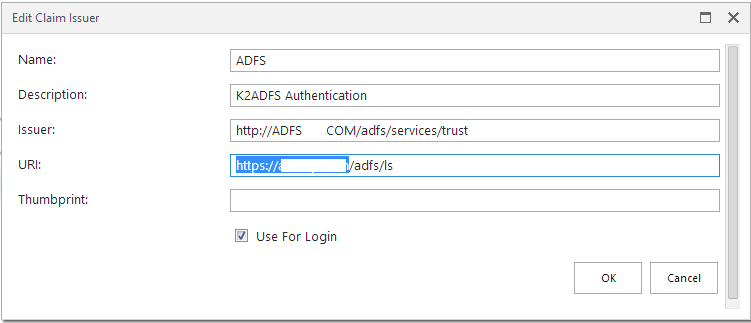
URI: This is composed of two parts
• Default root site ADFS binding
• SAML 2.0/WS-Federation endpoint
Step 2 (4.7 and up) - Update the Thumbprint in K2 using K2 Management:
- Open K2 Management
- Browse to the following location using the left-hand-side navigation panel: -- K2 Management > Authentication > Claims > Issuers - Select the issuer in question. Click the Edit button
- Update the thumbprint to the final copy created in Step 1 above
- It should be uppercase with no spaces
- There shouldn't be a need to restart the K2 service, but if you don't see any immediate changes, you can restart the K2 Service and do an IISRESET.
Step 3 - Verifying the Thumbprint in the K2 Database
- Open Microsoft SQL Server Management Studio and browse to your K2 Database
Option (By script):
Execute the following script on the K2 Database:
To find the good Id, you can execute the following query:
- Double-check it has been updated by right-clicking on the Table and choosing "Select Top 1000 Rows"
To resolve this issue, direct database modification will be required. Please log a K2 Support Ticket on the K2 Customer Portal for assistance in resolving the issue.


